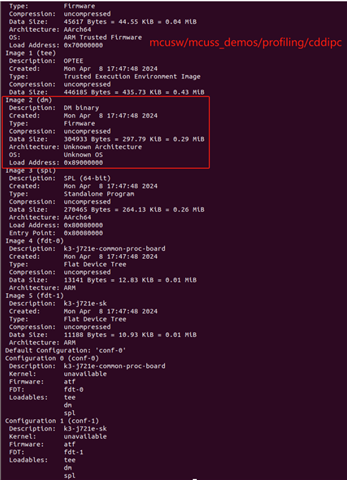
We are facing some issues while trying to replace the default demo application(mcusw->mcuss_demos->profiling->can or mcusw->mcuss_demos->profiling->cddipc)embedded in `tispl.bin` with another fw from SDK 9.0 (ti-processor-sdk-rtos-j721e-evm-09_00_00_02) like the compiled from any mcusw demo version (compiled to run in mcu1_0).
After generate the u-boot from Linux SDK 9.0 (ti-processor-sdk-rtos-j721e-evm-09_00_00_02) we set booting mode in DFU and pass the generated images, obtaining the following output after load the new `tispl.bin
1.The log of mcusw->mcuss_demos->profiling->can as follows
U-Boot SPL 2023.04 (Apr 02 2024 - 10:29:21 +0800)
SYSFW ABI: 3.1 (firmware rev 0x0009 '9.0.6--v09.00.06 (Kool Koala)')
EEPROM not available at 0x50, trying to read at 0x51
Reading on-board EEPROM at 0x51 failed -121
Trying to boot from MMC2
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Loading Environment from nowhere... OK
2.The log of mcusw->mcuss_demos->profiling->cddipc as follows
U-Boot SPL 2023.04 (Apr 01 2024 - 14:53:34 +0800)
SYSFW ABI: 3.1 (firmware rev 0x0009 '9.0.6--v09.00.06 (Kool Koala)')
EEPROM not available at 0x50, trying to read at 0x51
Reading on-board EEPROM at 0x51 failed -121
Trying to boot from MMC2
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Warning: Detected image signing certificate on GP device. Skipping certificate to prevent boot failure. This will fail if the image was also encrypted
Loading Environment from nowhere... OK
Starting ATF on ARM64 core...
NOTICE: BL31: v2.8(release):v2.8-226-g2fcd408bb3-dirty
NOTICE: BL31: Built : 00:42:57, Jan 13 2023
I/TC:
I/TC: OP-TEE version: 3.20.0 (gcc version 11.3.0 (GCC)) #1 Fri Jan 20 15:42:54 UTC 2023 aarch64
I/TC: WARNING: This OP-TEE configuration might be insecure!
I/TC: WARNING: Please check https://optee.readthedocs.io/en/latest/architecture/porting_guidelines.html
I/TC: Primary CPU initializing
I/TC: SYSFW ABI: 3.1 (firmware rev 0x0009 '9.0.6--v09.00.06 (Kool Koala)')
I/TC: HUK Initialized
E/TC:0 0 k3_sec_proxy_verify_thread:108 Queue is busy
E/TC:0 0 k3_sec_proxy_recv:196 Thread SEC_PROXY_RESPONSE_THREAD verification failed. ret = -65523
E/TC:0 0 ti_sci_get_response:101 Message receive failed (-65523)
E/TC:0 0 ti_sci_do_xfer:150 Failed to get response (-65523)
E/TC:0 0 sa2ul_init:59 Failed to get SA2UL device
E/TC:0 0 call_initcalls:43 Initcall __text_start + 0x00067bf8 failed
I/TC: Primary CPU switching to normal world boot
E/TC:0 0
E/TC:0 0 Core data-abort at address 0x10 (translation fault)
E/TC:0 0 esr 0x96000005 ttbr0 0x9e898000 ttbr1 0x00000000 cidr 0x0
E/TC:0 0 cpu #0 cpsr 0x800003c4
E/TC:0 0 x0 0000000000000010 x1 0000000000000001
E/TC:0 0 x2 0000000000000000 x3 0000000000000000
E/TC:0 0 x4 000000009e86c000 x5 0000000000ffffff
E/TC:0 0 x6 0000000000000002 x7 000000009e8a0190
E/TC:0 0 x8 0000000000000020 x9 000000009e8a0190
E/TC:0 0 x10 0000000000000000 x11 0000000000000000
E/TC:0 0 x12 0000000000000000 x13 000000009e8618f0
E/TC:0 0 x14 0000000000000000 x15 0000000000000000
E/TC:0 0 x16 000000009e8149e4 x17 0000000000000000
E/TC:0 0 x18 0000000000000000 x19 000000009e8a2ca0
E/TC:0 0 x20 000000009e8a2ca8 x21 0000000000000007
E/TC:0 0 x22 000000009e878000 x23 000000009e878b50
E/TC:0 0 x24 0000000100000000 x25 0000000000000000
E/TC:0 0 x26 0000000000000000 x27 0000000000000000
E/TC:0 0 x28 0000000000000000 x29 000000009e8a2c30
E/TC:0 0 x30 000000009e80eb7c elr 000000009e80eb9c
E/TC:0 0 sp_el0 000000009e8a2c30
E/TC:0 0 TEE load address @ 0x9e800000
E/TC:0 0 Call stack:
E/TC:0 0 0x9e80eb9c
E/TC:0 0 Panic 'unhandled pageable abort' at core/arch/arm/kernel/abort.c:572 <abort_handler>
E/TC:0 0 TEE load address @ 0x9e800000
E/TC:0 0 Call stack:
E/TC:0 0 0x9e808b04
E/TC:0 0 0x9e815f88
E/TC:0 0 0x9e808260
E/TC:0 0 0x9e805584